Phil Zimmermann created Pretty Good Privacy in 1991 and gave it away for free. The US government considered strong encryption to be a munition under the same laws that regulated missiles and tanks. Zimmermann distributed PGP anyway, uploading it to Usenet and bulletin board systems where anyone could download it.
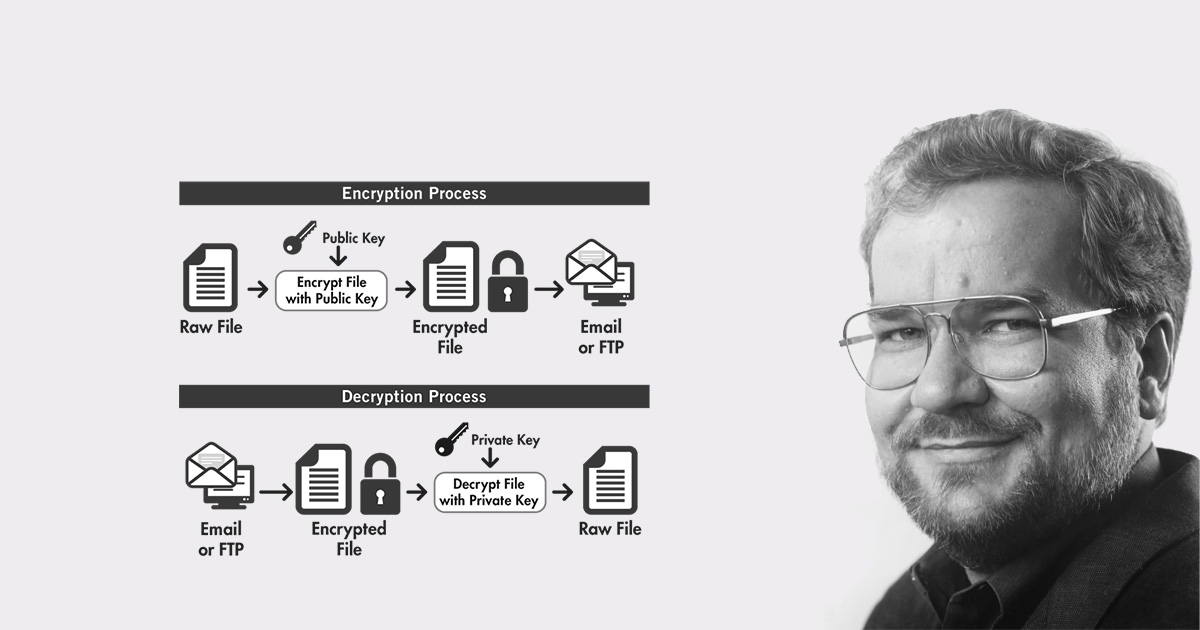
PGP was one of the first widely available strong encryption software tools that ordinary people could actually use. Before PGP, public-key cryptography existed but remained largely confined to academic papers and government agencies. Zimmermann took RSA encryption, combined it with symmetric ciphers, and built software that let anyone encrypt their email with keys that were computationally infeasible to break with known methods. He made it free. He made it accessible.
The government opened a criminal investigation in 1993. Zimmermann faced potential charges for "exporting munitions without a licence" because PGP spread internationally. The State Department classified strong encryption as a weapon under the International Traffic in Arms Regulations. Exporting weapons without authorisation carried prison time. Zimmermann's crime was writing software that protected privacy.
"I wanted to make it possible for ordinary people to communicate in private without the government listening in," Zimmermann said in interviews after the investigation began. "I thought that was important enough to take the risk."
The investigation lasted three years. During that time, Zimmermann and his supporters published the complete PGP source code in a printed book. Books are protected speech under the First Amendment. The government couldn't ban a book without admitting encryption was speech, not weapons. Anyone could buy the book, scan the pages, and reconstruct working PGP software.
In 1996, the Justice Department dropped the investigation without filing charges. By then, PGP had spread to over 60 countries. Millions of people used it. Journalists, activists, dissidents, and ordinary people who wanted private communication had access to strong encryption.
"If privacy is outlawed, only outlaws will have privacy," Zimmermann wrote in the PGP documentation. "Intelligence agencies have access to good cryptographic technology. So do the big arms and drug traffickers. So do defence contractors, oil companies, and other corporate giants. But ordinary people and grassroots political organisations mostly have not had access to affordable military-grade public-key cryptographic technology. Until now."
PGP proved that strong encryption could exist outside government control. Modern systems build on the same foundations. Signal uses end-to-end encryption. WhatsApp adopted Signal's protocol. ProtonMail offers encrypted email. Tor enables anonymous browsing. These systems exist in part because Zimmermann showed that encryption could be distributed globally and used by ordinary people without central control.
Governments are still pushing for ways to access encrypted communications. The EARN IT Act proposes scanning encrypted messages. The EU's chat control proposal demands client-side scanning of private communications. Australia's Assistance and Access Act 2018 compels companies to build access mechanisms. The UK's Online Safety Bill threatens end-to-end encryption.
Zimmermann's fight in the 1990s contributed to the legal and political shift toward treating encryption as protected speech rather than a controlled weapon. That foundation supports modern encrypted platforms today. Governments can demand access, but they cannot realistically eliminate the underlying mathematics.
"I figured it was only a matter of time before strong encryption became widely available, and it seemed better to release it early than wait for restrictions," Zimmermann explained. Governments worldwide proposed encryption controls throughout the 1990s. Many failed in part because PGP had already spread and was widely used.
Phil Zimmermann gave ordinary people access to the same class of cryptographic tools that had previously been restricted. He faced a criminal investigation for three years and distributed PGP globally before tighter controls could take hold. End-to-end encryption as it exists today owes a lot to that decision.
Blackout VPN exists because privacy is a right. Your first name is too much information for us.
Keep learning
FAQ
What is PGP?
Pretty Good Privacy is encryption software Phil Zimmermann created in 1991 that let ordinary people encrypt email with keys that were computationally infeasible to break with known methods. It was one of the first widely available strong encryption tools.
Why did the government investigate Zimmermann?
The US government classified strong encryption as a munition under the International Traffic in Arms Regulations. When PGP spread internationally, the government opened a criminal investigation in 1993 for "exporting munitions without a licence." The investigation lasted three years and no charges were filed.
How did Zimmermann fight the investigation?
Zimmermann and his supporters published the complete PGP source code in a printed book. Books are protected speech under the First Amendment. The government couldn't ban a book without admitting encryption was speech, not weapons.
What encryption systems descended from PGP?
Signal, WhatsApp, ProtonMail, and Tor all build on foundations established by PGP. These systems use end-to-end encryption and exist in part because Zimmermann showed encryption could be distributed globally and used by ordinary people without central control.
Are governments still trying to control encryption?
Yes. The EARN IT Act proposes scanning encrypted messages. The EU's chat control proposal demands client-side scanning. Australia's Assistance and Access Act 2018 compels companies to build access mechanisms. The UK's Online Safety Bill threatens end-to-end encryption.