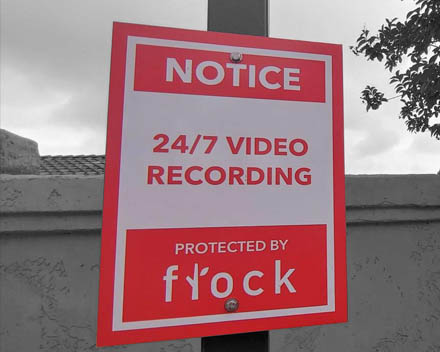
Another Surveillance Company the US Government Doesn't Have to Disclose
A Mexican surveillance company has built the infrastructure to watch 26 of Mexico's 32 states and is sharing that data in real time with the FBI, ICE, CBP, DEA, and ATF under a formal agreement signed in 2022. Because Seguritech is a foreign private company, no US transparency law reaches it.
Read more