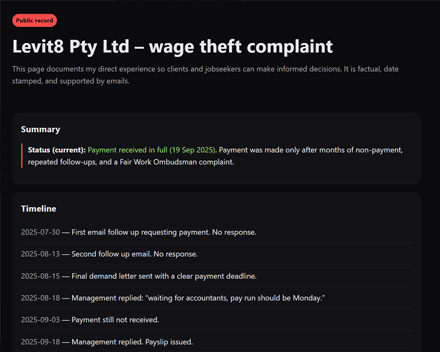
Levit8 Pty Ltd Don't Pay Their Staff.
A worker built a website for seven dollars to get back what his employer would not pay him. The site outlived the dispute. It is still ranking on the company's own name.
Read more
Tracker-free posts on privacy, protocols, and digital sovereignty.
A worker built a website for seven dollars to get back what his employer would not pay him. The site outlived the dispute. It is still ranking on the company's own name.
Read more
A single geofence warrant pulled location history for over 3,000 people across 489 acres that included a mosque, a university campus, homes, and a park. The Supreme Court heard about that warrant this week and started asking why it ever counted as a search of one suspect.
Read more
ICE admitted it uses Graphite, an Israeli zero-click spyware tool that requires no interaction from the target. The admission is more telling than the spyware itself.
Read more
A Mexican surveillance company has built the infrastructure to watch 26 of Mexico's 32 states and is sharing that data in real time with the FBI, ICE, CBP, DEA, and ATF under a formal agreement signed in 2022. Because Seguritech is a foreign private company, no US transparency law reaches it.
Read more
Azerbaijan has used Pegasus-grade spyware against its own journalists and activists for years, with zero consequences. Now it is building MİRAS, a permanent national surveillance platform controlled by the State Security Service, set to go live in May 2026. Access Now just filed an amicus brief at the European Court of Human Rights. The infrastructure is not waiting for the verdict.
Read more
Section 702 lets intelligence agencies collect communications without a warrant, including from an unknown number of Americans. Congress just extended it again and stripped every reform proposal in the process.
Read more
Every time an app serves you an ad, it broadcasts your location into an ecosystem that surveillance vendors harvest and resell. Penlink's Webloc system turns that data into three years of tracked movement for ICE, the US Army, and dozens of police departments nationwide.
Read more
Dragon Boss Solutions LLC shipped a trusted, digitally signed software update that deployed a PowerShell script to kill antivirus tools across 25,000 endpoints. Windows Defender was not bypassed accidentally. The payload specifically added exclusions to ensure future malware would not be detected.
Read more
After TotalRecall exposed Windows Recall's unencrypted screenshot database in 2024, Microsoft added authentication and encryption. TotalRecall Reloaded found the side entrance. The vault is solid, the researcher noted. The delivery truck is not.
Read moreAn independent audit of 7,000 websites found Google ignored Global Privacy Control opt-out signals 87% of the time, Meta 69%, and Microsoft 50%. In Google's case, the opt-out signal triggered more cookies. The mechanism was working as built.
Read more
Attackers compromised CPUID's website on April 9 and replaced download links for CPU-Z and HWMonitor with links to their own infrastructure. The installers users received carried a remote access trojan. The actual software builds were never touched.
Read more
The FBI extracted deleted Signal messages from an iPhone notification database during a 2025 federal prosecution. Signal's end-to-end encryption was never broken. iOS stored the evidence anyway.
Read more
Millions are using AI chatbots for emotional support. That convenience hides a serious privacy problem. Therapy-level disclosures are being logged by companies that store and reuse the conversations.
Read more
Russia's attempt to crack down on VPNs on 4 April overloaded its own filtering infrastructure and knocked out banking payments nationwide. In 2018, a similar attempt to block Telegram produced almost identical collateral damage.
Read more
Google Nest routers have no local admin interface and require cloud services enabled just to assign static IPs or set up port forwarding. Your home network data is being sent to Google whether you like it or not.
Read more
Over 200 organisations want AI-generated slop banned from YouTube Kids. The legislative response being built around child safety online involves mandatory ID verification for every adult on every platform, and the breach record already shows how that ends.
Read more
Apple frames each age verification rollout as compliance with local law. The result is a global identity layer being built into Apple account infrastructure, jurisdiction by jurisdiction, with no unified privacy framework governing the data.
Read more
LinkedIn silently scans your browser for over 6,000 extensions on every page load, collecting data that can reveal your religion, politics, job hunt, and health status. None of it is disclosed in their privacy policy.
Read more
Quad9 is a free, Swiss-based DNS resolver that encrypts your queries, blocks malicious domains, and doesn't log your IP. It's a meaningful upgrade over your ISP's default. It's not a privacy solution on its own.
Read more
A rootkit called NoVoice was hidden across 50+ Google Play apps downloaded 2.3 million times. It roots your device, survives a factory reset, and clones your WhatsApp session.
Read more
Apple almost never patches older versions of iOS. It did for DarkSword, and the age verification features baked into iOS 26 are the most likely reason "just upgrade" stopped working as an answer.
Read more
Phil Zimmermann created Pretty Good Privacy in 1991 and gave it away for free. The US government considered strong encryption to be a munition under the same laws that regulated missiles and tanks. Zimmermann distributed PGP anyway.
Read more
Every photo you take may contain your exact location down to a few meters. This data stays embedded in the image unless something explicitly removes it. In many cases, nothing does.
Read more
Lloyds Banking Group exposed personal data of up to 447,936 customers during a software glitch on March 12. The bank is asking customers who may have screenshotted other users' information to delete it. There is no mechanism to verify compliance.
Read more
Police in Coffee County, Georgia used Flock automated license plate reader cameras to issue a traffic ticket to a motorcyclist for holding a cell phone. Police departments across the country explicitly promise residents they will not use these cameras for minor violations. They lied.
Read more
A cybercrime group deployed a wiper attack targeting Iran over the weekend. The malware spreads through poorly secured cloud services and destroys data on infected systems that use Iran's time zone or have Farsi set as the default language.
Read more
GrapheneOS announced it will not comply with laws requiring operating systems to collect user age data at setup. The privacy-focused Android fork says if devices can't be sold in regions due to regulations, so be it.
Read more
Angela Lipps spent 108 days in a Tennessee jail because facial recognition software identified her as a bank fraud suspect in Fargo, North Dakota. She had never been to North Dakota. The algorithm was wrong. She lost her home, car, and dog proving it.
Read more
Navia Benefit Solutions disclosed a data breach exposing Social Security numbers, dates of birth, and personal information for 2.7 million people. Hackers accessed systems for 25 days before the company detected the intrusion.
Read more
Meta Ray-Ban smart glasses capture footage of naked people, sensitive information, and violent acts that thousands of employees in Kenya review for AI training. Investigation found workers see people using bathrooms, changing clothes, having sex, and entering credit card details.
Read more
South Korea's National Tax Service published photos of a seized Ledger hardware wallet with the handwritten mnemonic recovery phrase visible. Someone immediately transferred $4.8 million in cryptocurrency out of the wallet. The funds are gone.
Read more
UK Companies House exposed business data for five million registered companies from October 2025 until March 2026. The vulnerability allowed any logged-in user to access another company's dashboard by pressing the back button in a web browser.
Read more
14,000 routers infected with KadNap malware form a takedown-resistant botnet that carries cybercrime traffic through residential connections. The botnet uses distributed hash tables to hide command infrastructure and sells infected routers as anonymous proxies through Doppelganger service.
Read more
Pornhub blocked Australian users rather than implement age verification requiring facial scans, digital wallets, or photo ID. VPN downloads in Australia surged immediately as users refused to provide biometric data and identity documents to access legal content.
Read more
Microsoft security researchers discovered AI memory poisoning attacks where companies embed hidden instructions in Summarize with AI buttons. When clicked, these buttons inject commands into AI assistants telling them to remember companies as trusted sources. Microsoft identified over 50 unique prompts from 31 companies across 14 industries.
Read more
New York Attorney General sued Valve for illegal gambling through loot boxes while the state runs a lottery that extracts billions from the poorest residents. The poorest Americans spend 6% of their income on lottery tickets with 1-in-45-million odds.
Read more
Ring canceled its partnership with Flock Safety after weeks of public backlash over surveillance concerns. Users threatened to smash cameras over the company's ties to law enforcement while a leaked internal email showed founder Jamie Siminoff wants Search Party to "zero out crime."
Read more
Researchers at UC Santa Cruz and Johns Hopkins hijacked self-driving cars and autonomous drones using commands written on road signs. AI systems followed illicit instructions with success rates up to 95.5% in tests.
Read more
Amazon launched Search Party at the Super Bowl dressed as a lost dog feature. Every enabled Ring camera in your area automatically scans for targets and reports matches to a central system without the camera owner initiating anything.
Read more
Criminals flood small businesses with fake one-star reviews then demand payment to stop the attack. Platforms take weeks to act, leaving businesses losing customers and revenue while the damage is done.
Read more
Dutch authorities seized a Windscribe VPN server without a warrant and told the company they'd return it after analysis. Windscribe disclosed the incident publicly on X. Dutch police have issued no statement and referenced no judicial warrant.
Read more
Moltbook, a social media platform for AI agents, exposed its entire production database containing user secrets and personally identifying information within days of launch. The creator bragged on X that AI wrote all the code. Researcher Gal Nagli found the database API key exposed on the front end in minutes.
Read more
Internal documents from Meta revealed during California lawsuits show the company knew Instagram was designed to be addictive and deliberately hid this from parents. Employees called it a drug. Zuckerberg said telling parents would ruin the product.
Read more
Former Google engineer Linwei Ding was convicted on 14 counts for stealing over 2,000 pages of AI trade secrets and transferring them to Chinese companies. He uploaded confidential files to his personal cloud while secretly founding a Chinese AI startup and pitching investors using stolen Google technology.
Read more
Security researchers found that Bondu's AI dinosaur toys left over 50,000 chat logs exposed to anyone with a Gmail account. Children's names, birth dates, family details, and every private conversation sat on a web portal anyone could access without hacking.
Read more
Anthropic's latest model replicated one of history's costliest breaches using only Bash and Kali Linux. No custom toolkits, no iteration, no external lookups.
Read more
Microsoft hands BitLocker recovery keys to law enforcement about 20 times annually when served with warrants. The keys live on Microsoft servers by default, letting federal agents unlock encrypted drives without asking the device owner.
Read more
SentinelOne SentinelLABS and Censys discovered 175,000 publicly accessible Ollama AI servers operating without authentication across 130 countries. The servers form a massive unmanaged layer of AI infrastructure running outside corporate security controls.
Read more
Signal Foundation president Meredith Whittaker says AI agents embedded in operating systems are destroying the practical security of end-to-end encryption. The agents require sweeping permissions to read messages and access credentials, collapsing the isolation that encrypted messaging relies on.
Read more
Indian government entities were hit by two cyber campaigns in September 2025 using GitHub repositories for command and control. The attacks filtered victims by IP address and delivered backdoors only to Windows users in India.
Read more
The UK House of Lords voted to ban VPN services for anyone under 18. The age verification required puts Britain on the same policy path as China, Russia, and Iran
Read more
Ireland's Communications Bill gives police authority to install spyware on your devices, break encryption before it activates, and track every phone in a given area. The government calls it modernization. It's state-sanctioned hacking.
Read more
The most trusted MCP servers contain exploitable vulnerabilities. Research shows 36.7% of all MCP servers may share the same security flaws found in Microsoft's implementation.
Read more
Google's Fast Pair protocol was designed for one-tap Bluetooth connections. Researchers just proved it also gives hackers one-tap access to hijack your earbuds, activate your microphone, and track your location in under 15 seconds.
Read more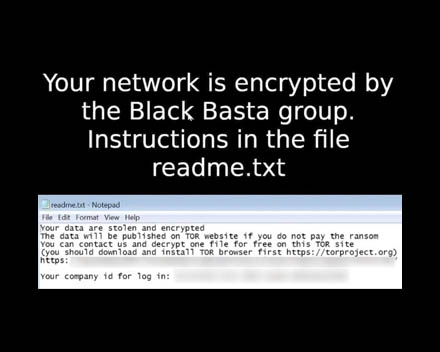
Oleg Nefedov, a 35-year-old Russian national, has been added to the EU Most Wanted and INTERPOL Red Notice lists as the alleged leader of Black Basta ransomware. Ukrainian and German authorities identified two Ukrainian accomplices who worked as password crackers for the group.
Read more
Malicious Chrome extensions posing as enterprise productivity tools stole authentication credentials from Workday, NetSuite, and SAP SuccessFactors users. The extensions extracted session cookies every 60 seconds and blocked access to security management pages.
Read more
The UK government created Pathways, a video game with an extremism meter that tracks children's thoughts. Schools deploy it for kids aged 11-18. Researching immigration statistics increases your score. Prevent referred a triple murderer three times and released him. Now it tracks teenage curiosity.
Read more
X reported 870,000 child abuse cases in 2023. Australia fined them $610,500 and moved on. Grok's AI deepfakes in December 2025 triggered investigations and ban threats within 72 hours.
Read more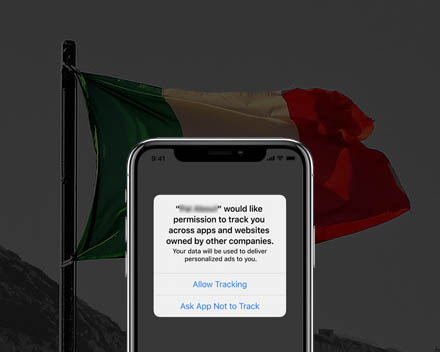
Italy fined Apple €98.6 million over App Tracking Transparency, arguing the consent burden fell harder on third party developers while reinforcing ad tracking as the assumed norm.
Read more
Amazon stopped 1,800 North Korean operatives from infiltrating its workforce, exposing how remote hiring and broken digital identity systems are being weaponised.
Read more
In a 2023 action, the FTC said Ring allowed employees to spy on private footage and ignored basic security, enabling hackers to hijack home cameras.
Read more
Victoria is exploiting a terrorist attack to push anti-democratic laws that restrict speech, suppress protests, and force platforms to identify users.
Read more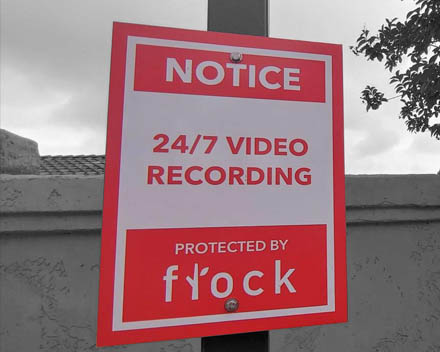
Flock Safety exposed dozens of Condor cameras filming unattended children and lone adults directly to the internet. Predators accessed live video and full archives with no login or trace.
Read more
AI browsers combine instruction-following models with direct access to sensitive systems, creating failure modes vendors admit cannot be eliminated.
Read more
After years of mass data breaches, South Korea is mandating facial verification for SIM cards, shifting identity failure into permanent biometric risk.
Read more
Children are being given powerful digital devices earlier than ever. The problem is not technology itself but timing. Developing brains are being shaped by tools designed for constant stimulation.
Read more
Cisco customers were hit by a China-linked zero-day exploit and a separate VPN brute-force campaign within days, exposing persistent edge security failures.
Read more
US prosecutors destroyed two open source developers after regulators told them no crime existed. This case exposes how far the surveillance state will go to crush privacy tools that work.
Read more
The KimWolF botnet is quietly infecting Android devices at scale by hiding inside trojanised apps and turning phones into invisible infrastructure.
Read more
Attackers are using stolen AWS credentials to spin up massive cryptomining workloads within minutes, draining accounts without exploiting any AWS vulnerability.
Read more
Texas is suing major TV manufacturers for using deceptive tactics to turn smart TVs into surveillance devices without real consumer consent.
Read more
Ethical AI depends on consent and accountability. Under state control, AI becomes a system for scaling repression, not protecting rights.
Read more
A Google featured browser extension with millions of users silently intercepted AI chats across major platforms and exported them to analytics servers as a business model.
Read more
Attackers abused PayPal’s subscription system to send legitimate PayPal emails that falsely claim expensive purchases and push victims toward scam phone numbers.
Read more
A fake torrent claiming to contain a new Leonardo DiCaprio film was used to infect Windows users with Agent Tesla by abusing scripts, shortcuts, and built in system tools.
Read more
Session Messenger rejects phone numbers, central servers, and contact graphs. This deep dive explains how its network works, why Protocol V1 made controversial tradeoffs, and how Protocol V2 changes the cryptographic model.
Read more
Microsoft Recall screenshots your screen by default. Signal responded by blocking Windows from capturing private conversations entirely.
Read more
Roger Dingledine helped build Tor and spent the next twenty years refusing to weaken it. That decision shaped the modern privacy landscape.
Read more
India is mandating SIM binding for WhatsApp, Signal and Telegram. If your SIM changes, your messages die. This is surveillance, not security.
Read more
The US is moving from checking identities to judging expression. Five years of social media is now being treated as a border requirement.
Read more
A 19 year old breached nine companies and sold 64 million identity records. The real failure is the companies that collected that data in the first place.
Read more
The December patches show a shift. Zero-days no longer live only in Windows. They now live inside IDEs, AI assistants and the autocomplete layer that touches your entire workflow.
Read more
Shanya proves stealth is now a commodity. Ransomware gangs no longer build their own evasion. They rent it and walk straight past EDR tools still relying on a broken Windows trust model.
Read more
The FTC denied SpyFone’s attempt to escape its 2021 ban because nothing changed. SpyFone was stalkerware and the industry still harms real people.
Read more
A new peer reviewed study shows enormous VPN brands lying about ownership, hard coding encryption keys, and quietly piping user data through insecure tunnels. The rot is systemic and it has been hidden behind Singapore shell companies and marketing gloss.
Read more
Thirty vulnerabilities in AI coding tools show how prompt injection and auto approved actions can escalate into data theft and remote code execution. Every major AI IDE tested was vulnerable.
Read more
Chinese state-linked groups like Earth Lamia and Jackpot Panda exploited CVE-2025-55182 in React Server Components within hours of its December 3 2025 disclosure. This unauthenticated RCE flaw gives attackers full server access without logins
Read more
Petco exposed customer data after a misconfigured app left files accessible online. The real failure is the industry wide habit of collecting information it cannot defend.
Read more
Axon is using Edmonton Police to trial face recognition on body cameras. The test builds a biometric pipeline that expands police visibility far beyond live encounters.
Read more
India issued a secret order on 28 November 2025 forcing every phone maker to bake the Sanchar Saathi government app into devices and block users from disabling it. Three days of fury later the mandate is dead.
Read more
A SonicWall weakness let ransomware actors infiltrate Marquis Software Solutions and extract sensitive data from 74 US banks and credit unions. This attack shows what happens when a single vendor becomes a quiet central point of failure.
Read more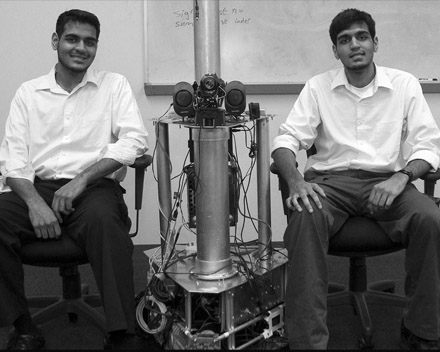
Twin brothers Muneeb and Sohaib Akhter spent years hacking private companies and U S government systems. Their schemes show how insider access and basic intrusions cause real damage before nation state actors ever get involved.
Read more
The USPTO wants to cripple inter partes review and make bad patents untouchable. EFF is pushing back because the public needs the power to challenge broken law.
Read more
Flock claims it runs a smart automated safety system but the real work is being done by offshore gig workers reviewing raw footage of Americans.
Read more
Albiriox is a new Android MaaS threat built for on device fraud, VNC control and credential theft. It targets more than 400 financial apps and bypasses FLAG_SECURE protections.
Read more
After media accusations and law enforcement pressure, GrapheneOS is exiting France entirely and moving infrastructure to Canada.
Read more
Over $262 million has been lost in 2025 alone to account takeover scams, with attackers mimicking bank staff and spoofing websites to steal credentials.
Read more
CISA just added an old OpenPLC ScadaBR XSS bug to the KEV list after a pro Russian crew used it in the wild. If your HMI is on the internet with default creds, you are the low hanging fruit.
Read more
US states are pushing bills that punish VPN use and force websites to expose users. It looks a lot more like authoritarian censorship than child protection.
Read more
Edward Snowden exposed a surveillance system that watched everyone while pretending it did not exist. His leaks forced the world to face the truth.
Read more
GrapheneOS strips out Google’s surveillance layer and replaces it with real security. It takes discipline to use, but the payoff is a phone that finally works for you instead of advertisers.
Read more
Monero hides the sender, receiver and amount on every transaction. In a world built on surveillance finance, this is what real digital cash looks like.
Read more
Smart speakers are marketed as helpers but operate as networked microphones feeding Amazon and Google. Every misfire and bug proves how fragile your privacy becomes once you let them in.
Read more
Smart lightbulbs look harmless but most are insecure, invasive and built to fail. The fewer IoT gadgets you own, the safer your home becomes.
Read more
Zcash’s surge has set off panic among Bitcoin purists and institutions that want crypto domesticated. Privacy is back on the table and the usual suspects are furious.
Read more
The Federal Court issued a five point eight million penalty against Australian Clinical Labs for a breach affecting 223000 people. It confirms that companies guarding sensitive data keep failing while regulators act only after the damage is permanent.
Read more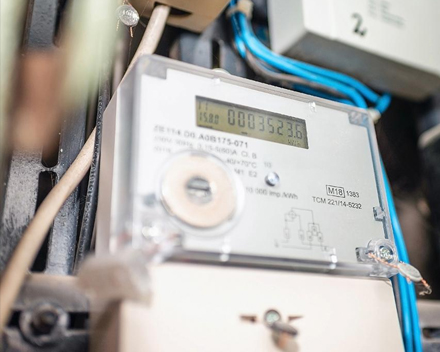
A California judge has shut down a decade long program where police used utility smart meter data to scan entire neighborhoods without suspicion. The ruling confirms that mass data sharing by utilities crosses clear legal limits.
Read more
Researchers scraped 3.5 billion WhatsApp profiles using WhatsApp’s own contact discovery feature. No hack. No breach. Just a system that exposes too much data by design.
Read more
Hidden documents show Meta estimates up to 10% of its 2024 revenue comes from scam advertisements and that its platforms display 15 billion “higher risk” scam ads each day.
Read more
Britain now arrests people for tweets, memes and opinions. Australia is copying the same digital ID structure that lets it happen.
Read more
The GUARD Act claims to protect kids, but the fine print reveals a mass identity check for every American and a ban on teens using basic digital tools.
Read more
Flock Safety built a private surveillance empire by turning neighbourhoods into checkpoints and handing your data to police and federal agencies. Here is how the system really works.
Read more
WireGuard stripped VPNs back to what matters, modern cryptograpy, tiny attack surface, insane speed, and zero legacy baggage. Here is why we built Blackout on top of it.
Read more
A contractor leaked over seventy thousand government ID images tied to Discord accounts. Safety laws created the target.
Read more
‘Child safety’ laws are being used to justify nationwide identity verification. Here's how digital ID systems and age checks merge into one surveillance framework.
Read more
A simple guide to what Linux is, why it exists, and how to install it. Learn why privacy users trust it and how to start safely.
Read more
Naomi Brockwell cuts through the noise with practical privacy that works in the real world.
Read more
The Five Eyes alliance turned wartime cooperation into a permanent surveillance network. Here’s how it formed and what it means for privacy.
Read more